The NCA has revealed details of an international disruption campaign targeting the world’s most harmful cyber-crime group, LockBit.
What is LockBit?
LockBit was considered the largest ransomware group in terms of impact globally, responsible for 25% of ransomware attacks in the last year (2023-2024).
LockBit were in operation for four years and during that time, attacks utilising their ransomware were prolific. LockBit ransomware attacks targeted thousands of victims around the world, including in the UK, and caused losses of billions; both in ransom payments and in the costs of recovery.
The group provided ransomware-as-a-service (RaaS) to a global network of hackers or ‘affiliates’, supplying them with the tools and infrastructure required to carry out attacks.
When a victim’s network was infected by LockBit’s malicious software, their data was stolen and their systems encrypted. A ransom would be demanded in cryptocurrency for the victim to decrypt their files and prevent their data from being published.
What we did
LockBit’s criminal enterprise was compromised in three strikes by: infiltrating their systems and obtaining their data, taking control, and locking them out.
Screenshot 1

Screenshot 2:

Screenshot 3:
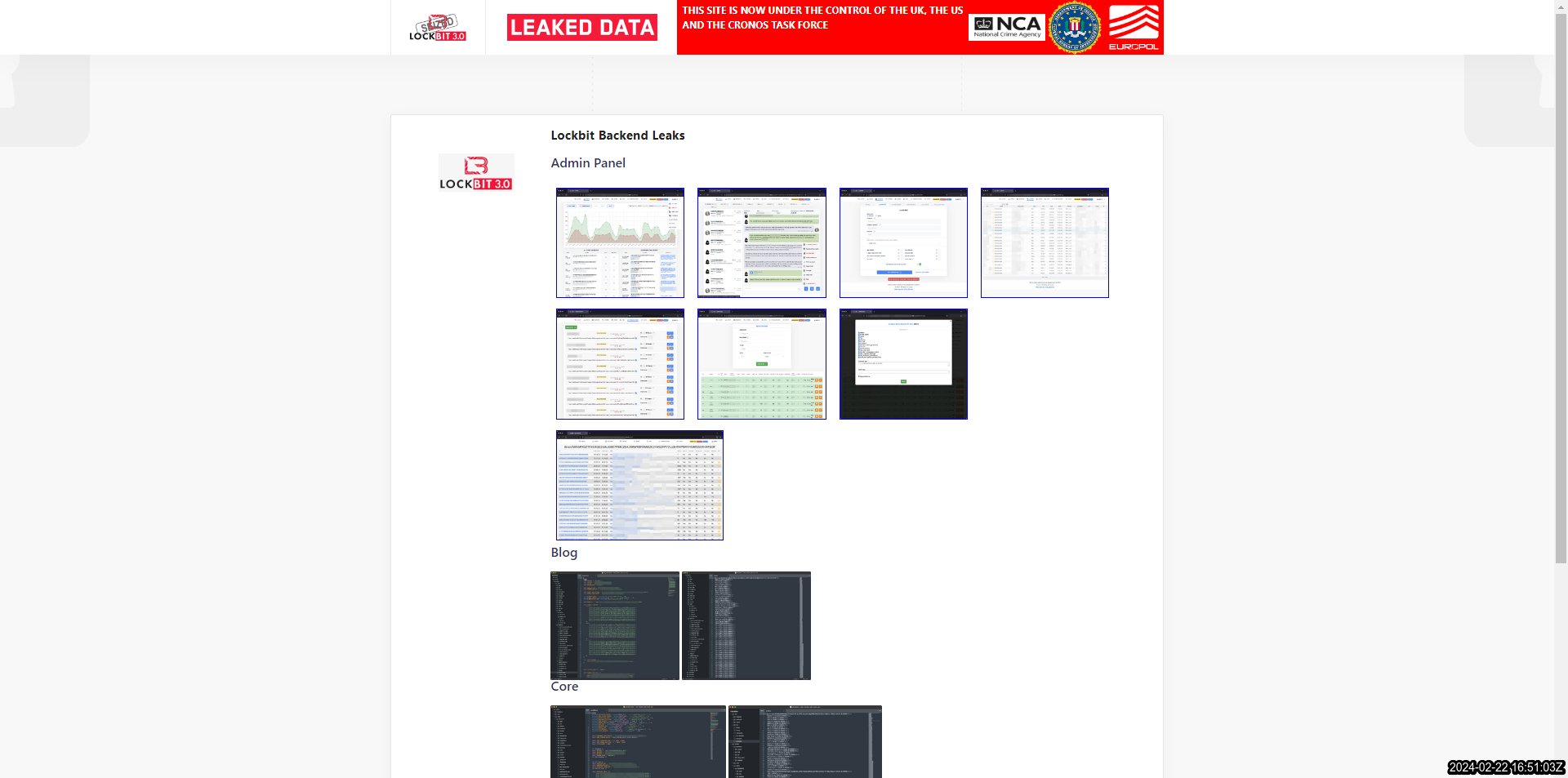
The NCA seized control of LockBit’s primary administration environment, which enabled affiliates to build and carry out attacks, and the group’s public-facing leak site on the dark web, on which they previously hosted, and threatened to publish data stolen from victims.
After infiltrating LockBit’s systems, information about their criminal activity and those who worked with them was also gathered. This included their network of 194 ‘affiliates’.
The Agency also obtained LockBit platform’s source code and a vast amount of intelligence from their systems about their activities and those who have worked with them and used their services to harm organisations throughout the world.

What we’re doing now
After seizing control, the leak site was redesigned by the NCA to instead host a series of articles exposing LockBit’s capability and operations.
Content was posted daily on a range of topics showing the extent of our access and included help for their victims as well.
At the end of the week, the leak site was then taken down completely.
Reporting
Public engagement is key to this response so it is vital that organisations report it, if they are the victim of a ransomware attack. The earlier the report, the faster the NCA and partners are able to assess new methodologies and limit the damage they can do to others.
If you are in the UK, you should use the Government’s Cyber Incident Signposting Site [link] as soon as possible for direction on which agencies to report your incident to.
If you’ve been impacted by LockBit, we now have 1,000 decryption keys taken from LockBit’s site to help you decrypt stolen data:
If you’re based in the UK, please email the NCA at – lockbit@nca.gov.uk
If you’re based in the US, please visit – https://lockbitvictims.ic3.gov/
If you’re based anywhere in the world other than the UK/US, please visit – https://www.nomoreransom.org/en/decryption-tools.html
Please provide the following information to support your case:
- Your company/organisation name and the domain attacked
- The decryption or description ID LockBit provided you with on the ransom note
- The date of the attack
- Whether you reported the case to law enforcement. If so, please provide the reference
- A contact name, email and telephone number





